New CERT-In Vulnerability Disclosure Program has a significant Disclaimer
The Computer Emergency Response Team- India (CERT-In) released its new ‘Responsible Vulnerability Disclosure and Coordination Policy’ today. The policy encompasses vulnerability reporting guidelines, coordination policy for resolution, some timeframes, reward policy, and a significant disclaimer.
What is CERT-IN?
Section 70B of the Information Technology Act, 2000, empowers CERT-In to handle issues relating to cyber security threats and coordinate with both public and private sector entities (including individuals). It conducts tracing and analysis of threats and also provides 24*7 incidence response services, besides proactively issuing guidelines, advisories, and take measures to prevent any cybersecurity breach.
Also read: What is Computer Emergency Response Team- India (CERT-In)?
What is a Vulnerability Disclosure Program?
To prevent cybersecurity breaches, to the Government of India’s infrastructure as well as private products, CERT-In collaborates with individual security researchers, academic institutions, cybersecurity teams, service providers, body corporates, and government organizations.
As such, multiple stakeholders from all over the world can report vulnerabilities that exist in information systems, which hackers could exploit to inflict damage to systems/ data, or even steal important data. The CERT-In rules also empower it to collect and analyze information from persons reporting any vulnerability in an information system.
Hence, CERT-In runs a responsible vulnerability disclosure program, which a policy governs.
Singapore has recently revised its vulnerability disclosure program and promises to reward hackers with up to $150,000 for reporting serious vulnerabilities.
Details of CERT-In’s Vulnerability Disclosure Policy
Reporting: Stakeholders can report vulnerabilities to CERT-In through email at vdisclose@cert-in.org.in. However, CERT-In only accepts reports PGP encrypted emails and attachments, for which it publishes its public keys.
Also read: What is asymmetric encryption and public key infrastructure?
Detailed Vulnerability Reports: The report shall include the details of the affected product, exact software version and model, vendor details, and a description/ details/ proof of vulnerability including steps to reproduce it.
Coordination for resolution: Once CERT-In receives a report, it will examine and validate the report. If the validation is successful, it will initiate coordination with the vendor and other stakeholders. Lastly, it will release vulnerability notes/ advisory.
Important Timelines: CERT-In says it will resolve the issue with 120 days from initial vendor contact (not the date of the disclosure). The timeline is relatively easy, but CERT-In says it will prioritize resolution depending upon the seriousness of vulnerability and if it’s being actively exploited.
Credits and Reward: CERT-In will give due credit to the person/organization who discloses the vulnerability on the vulnerability note/ advisory it will publish on its website. Regarding rewards, the Vendor may choose to reward the discloser. CERT-In will not participate in any discussions regarding the reward and will only introduce the vendor to the discloser.
The Disclaimer and its Importance
In order to report a vulnerability, any researcher/organization has to first find it. As such, the researcher will have to initiate a probe into an information system and document a proof of concept for exploiting the vulnerability.
However, the policy issues a significant disclaimer:
“The reporting party must ensure to comply with all the extant laws and regulations while discovering the vulnerabilities. Reporting a vulnerability to CERT-In does not imply being exempt from compliance. Disclosure shall be responsible for any action performed by her/ him for discovering the vulnerability whatsoever.”
Simply meaning- security researchers need to comply with the laws of the land while discovering the vulnerability. This is a bit problematic since such research/ probing involves ‘unauthorized access’ to the information system to some extent- a crime under Section 43 of the IT Act. It opens up avenues of wrongful prosecution.
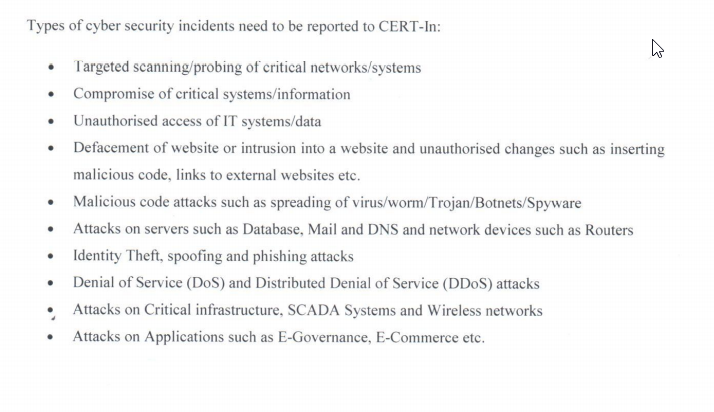
Further, the CERT-In rules require organizations to mandatorily report several types of cyber security incidents (refer to the image below). This Annexure mandates that organizations must report even targeted scanning/ probing of critical networks.
Cybersecurity research and discovering vulnerabilities is a walk on a tight rope. It is the intent (Section 66) of a person, which differentiates a white hat hacker from a black hat. However, in absence of standardized processes, robust communication protocols, and participation programs, security researchers may face wrongful prosecution. Even though it may not result in a conviction, lengthy prosecution and bad repute will most certainly deter white hat hackers from responsible disclosure or even force them to leave the trade altogether.
Do subscribe to our Telegram channel for more resources and discussions on tech-law. To receive weekly updates, don’t forget to subscribe to our Newsletter.